Proper security is the basis for the success of any application development, regardless of industry and field of application. The security of Learning Management Systems has evolved in response to the demand for its security features. The modernization of the training space ensures equal access to participants in the educational process regardless of their place of residence and form of education. The flexibility of LMS has increased popularity with its integration with LDAP/SSO/CAS authentication and with any other platform (ex: ERP, CMS, Peoplesoft, stripe, payment gateway).
The problems in LMS come from authentication, confidentiality, integrity, and availability type of attack.
Authentication attacks:
Today, the most critical vulnerabilities occur when authentication breaks and the identity of a legitimate end user gets robbed. The credential management functions (remember my password, forgot my password, change my password, etc.) and session tokens are not often protected accurately. Furthermore, attackers can intercept and steal authenticated sessions of a legitimate user.
The other vulnerabilities occur with insecure communications that impact transmits of sensitive information (session tokens) without proper encryption. An attacker can misuse this flaw to impersonate users and access unprotected conversations.
Solution 1: Single sign-on authentication scheme:
It is the roadmap for potent security and access management systems owning to the user experience. MFA (Multi-factor authentication) is a great way to authenticate them through push messages, One-time passwords, and QR codes. It gives an extra layer of protection before authorizing them to use applications. Also, it has a better access management system that lets all the multiple applications log in via a mobile token. Integrating moodle with SSO helps add extra protection to its users. One has to balance the enterprise security risk owning to the user convenience.
Adopt an identity service provider to strengthen LMS security by allowing users to enter a code sent to their phone for authorization. The advantage of SSO is improving ease of access with simplified username and password management without needing to remember passwords for multiple applications.
Solution 2: Using unique password patterns:
You can add these settings on your LMS platforms to reduce the risk of your site growth.
Password length
Number of digits
Number of lowercase letters
Number of uppercase letters
Number of non-alphanumeric characters
Number of consecutive identical characters
Reuse and rotation of passwords
Confidentiality attacks:
Confidentiality attacks allow unauthorized access to confidential resources and data. The main intention of the attacker is not data modification but data access and dissemination. The sensitive information does not have appropriate encryption leads to other confidentiality flaws of insecure cryptographic storage.
LMS systems rarely use cryptographic functions properly to protect data and credentials or use weak encryption algorithms. In both situations, valuable data is relatively easy to access by an attacker who can conduct identity theft and similar crimes.
Next, vulnerability occurs when LMS uses object references (like files, database records, and primary keys that represent either by URL or form parameters) directly in web interfaces without authorization.
The risk of unneeded information through error messages can leak sensitive information about its logic, configuration, and other internal details (SQL syntax, source code, etc.). On the other hand, error messages that LMS display have too much information that may be useful to attackers in privacy violations or conducting even more severe attacks.
Solution 1: Disable development settings
Having Debug messages enabled on the production site could expose information on the site. The CRON exceptions without a CRON password can also be a security threat. The additional settings tab relative to “Open to Google settings” or “Open to search engine” can allow confidential information to leak via Google search results.
Solution 2: Account management
Due to the increasing demand for speed of technological change, the risks can be a double-edged sword. So a thoughtful approach is required to security and privacy. You can achieve this while granting permissions to both software applications and eLearning courses in terms of their use. Use a valid email address for account creation, or rather create user accounts to be managed by a single system to avoid unnecessary complexities and risks.

Solution 3: Roles and permissions capabilities
Good role management on your LMS can reduce many headaches of the site administrators; as a best practice, you can assign roles and permissions to the users who need them.
Availability attacks:
Availability attacks misuse finite bandwidth and connectivity resources of the LMS system. DoS attacks usually result in a user’s incautious behavior. There are two general types of DoS attacks: logic and flooding attacks. Logic attacks (ping)exploit existing LMS flaws to crash remote servers or significantly decrease performance. Flooding attacks overload LMS with requests to disable legitimate users from accessing e-learning resources. DoS attacks present a threat to LMS systems because one request replicates by many participants needed to find the particular solution.
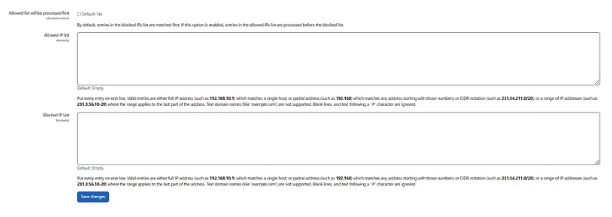
Solution 1: IP blocker
The list of IPs allowed for using LMS and blocked can be added here. The entries with permissions will be processed first, then the blocked IP list next.
Solution 2: HTTP security
Enable sending of secure cookies to HTTPS connections only to prevent spam messages.

Conclusion
The above security settings are just a few. Running your security option also includes maximum uploaded size, profile visible roles, choosing the amount of data that each user can store in their private files area, the time taken to validate password reset requests, requiring an email confirmation step when users change their email address in their profile, prevent users from entering a space or line break only in required fields in forms. And many more. Get going with secure connections and get rid of your upcoming damage.
Guest article written by:  Parul Sagar. Technical Writer. She has experience building a large audience-based, readily comprehensible text that focuses on page views, clicks, and lead generation. I’m a firm believer in ongoing development.
Parul Sagar. Technical Writer. She has experience building a large audience-based, readily comprehensible text that focuses on page views, clicks, and lead generation. I’m a firm believer in ongoing development.

